How to HODL | Finding The Best Crypto Wallet for You

The crypto community was once again reminded this month of its most central maxim: “Not your keys, not your crypto.” As bitcoin and the broader crypto market have experienced severe drawdowns, Celsius, a large, custodial crypto lender, has halted customer withdrawals citing “extreme market conditions.” Meanwhile, Binance temporarily halted BTC withdrawals due to a “stuck transaction causing a backlog.”
So now seems like a particularly good time to take a step back and re-access how to HODL crypto. While “Not your keys, not your crypto” is technically correct, this approach is likely not the best strategy for everyone. In contrast, most high net-worth individuals and institutions have security needs beyond what’s offered from battle-tested, cold-storage wallets.
The point is individuals must think for themselves when determining the best crypto wallet(s) for their unique needs. So, let’s consider the basic wallet types and considerations:
Crypto Wallet Types & Considerations
Hot Wallets vs. Cold Wallets
- Hot Wallet: Always connected to the internet. Takes the form of a software wallet on a computer or smartphone (e.g. Guarda, MetaMask, etc).
- Cold Wallet: Exists offline. Takes the form of an external USB or Bluetooth device (e.g. Ledger Nano X).
Custodial Wallets vs. Non-Custodial Wallets
- Custodial Wallets: Third-party has possession of users’ private keys; and therefore has ultimate control over the assets (e.g. Coinbase).
- Non-Custodial Wallets: Users have possession of their private keys; and therefore users have ultimate control over their assets (e.g. Bitgo, Ledger Nano X, etc).
Crypto Wallet Considerations
- Control – Ability to access, transfer, and trade assets at any time.
- Convenience – Ease to access, transfer, and trade assets.
- Security – Degree of protection against mistakes, losses, hacks, and theft.
The 4 Quadrant Crypto Wallet Spectrum
These wallet types and considerations overlap and relate with each other. Thus, we can perceive everything in a 4 quadrant spectrum:
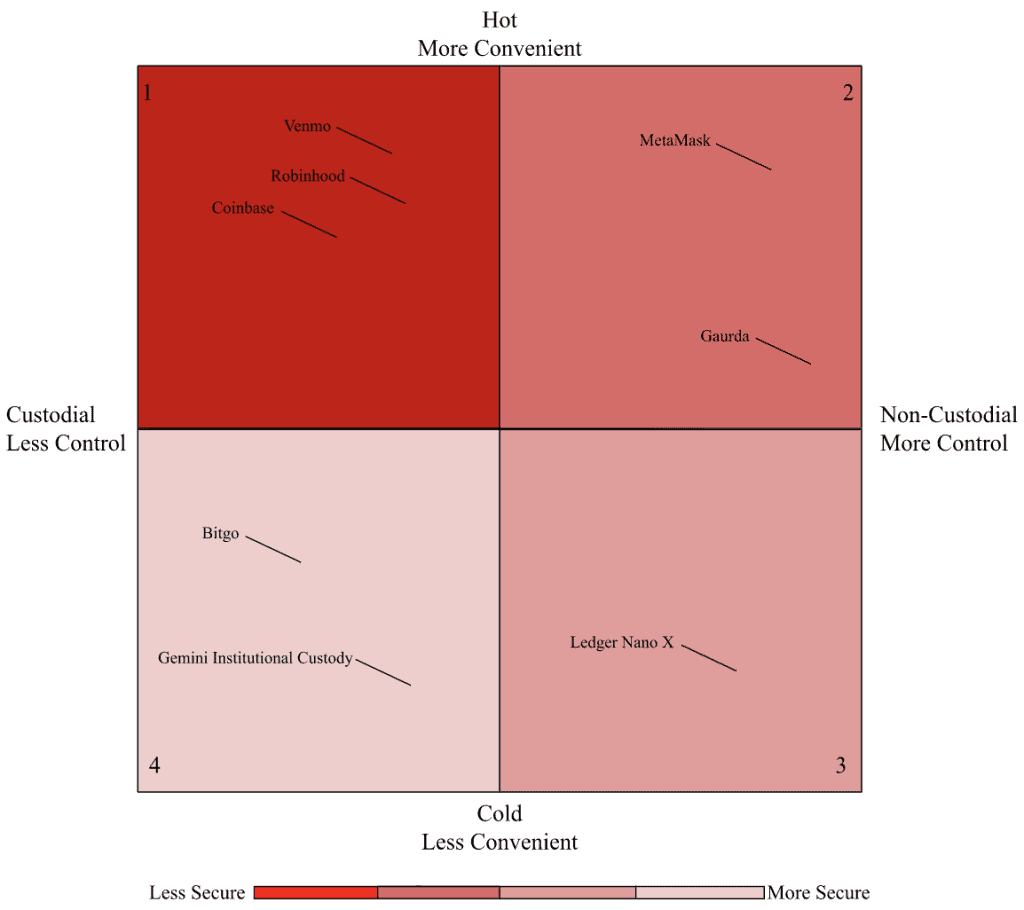
Let’s analyze each quadrant.
Quadrant 1 – Custodial Hot Wallets
Custodial hot wallets maximize convenience over all else.
- Convenience – Anyone who has a smartphone and wants to buy crypto (but just doesn’t know how) probably already has an app ready to go. Cash App, Venmo, and PayPal come to mind. These apps make crypto very easy to purchase and extremely liquid. Users can (generally) trade between cash and crypto twenty-four-seven.
- Control – Because corporate third-parties have possession of private keys, users are spared from making fatal mistakes and forever losing all their assets. Something never obtained (private keys) can never be lost. Users can always call customer support if they lock themselves out of their accounts.
- Downside – Third-parties having possession of private keys is they can ultimately do whatever they need with users’ assets. Those who dismiss this risk should see the links at the top of this article, and Coinbase’s SEC disclosure stating its right to withhold users’ assets in a bankruptcy event, thereby regarding users as general unsecured creditors. Companies will take extreme measures to survive when faced with a liquidity crisis.
- Security – Although 2FA has substantially helped, custodial hot wallets are still less secure than non-custodial hot wallets and cold wallets because custodial hot wallets are continually exposed to both insider threats and external hackers.
Quadrant 2 – Non-Custodial Hot Wallets
- Non-custodial hot wallets give users a high degree of convenience and full control with a security upgrade.
- Convenience – Non-custodial hot wallets can be quickly accessed with a few keyboard clicks, and most have built-in exchanges. Meaning users can trade from inside their wallets (but caution is warranted because trading fees can sometimes be more expensive compared to larger exchanges, due to exchange spread from third-party API providers).
- Control – Only users have possession over their private keys. This means users can anonymously access, transfer, and trade assets across the globe, twenty-four-seven. No adult supervision required! But caution is still necessary. If:
- someone gains access to a user’s private keys (via a hack or physical theft); OR,
- a user’s device is stolen / lost / breaks AND the user lost / forgot their private keys, then it’s game-over. Thanks for playing. All their assets are gone.
- Security – Non-custodial hot wallets are more secure than custodial hot wallets because the former are not exposed to insider threats. But non-custodial hot wallets are less secure than cold wallets because the former are always exposed to hackers, given these wallets are always connected to the internet.
Quadrant 3 – Non-Custodial Cold Wallets
Non-custodial cold wallets prioritize security and control over convenience.
Non-custodial cold wallets are more secure but less convenient than hot wallets because it’s extremely difficult for hackers to access cold wallets’ private keys, given they are stored offline.
But these wallets are therefore less convenient because they exist as physical devices (thumb-drives or bluetooth devices) unconnected from computers and the internet. Therefore, if users want to work with assets stored on these types of devices, they must first locate the device, and then connect it to a computer.
The same principles of control apply to both non-custodial cold and hot wallets. So, non-custodial cold wallets have the same control benefits and risks as non-custodial hot wallets, as detailed in the section above.
Quadrant 4 – Custodial Cold Wallets
Custodial cold wallets maximize security over all else.
Certain companies offer custodial cold storage solutions as white-glove business service offerings for high net-worth individuals, family offices, and institutions. When tens of millions to billions worth in assets must be secured, professional custodians are employed. These custodians utilize state-of-the-art, military-grade cold storage facilities in order to safely secure these assets.
Convenience is diminished because clients must generally issue an order to the custodians before assets can be handled. And although clients technically do not have ultimate control, their downside risk is likely very limited given the contractual relationship and legal recourse options between these types of clients and custodians.
Final Thoughts
There is no one size fits all when it comes to wallets. Individuals should perform self-assessments to determine which wallets best fit their needs. As users continue to increase their crypto knowledge and grow their assets, they typically end up utilizing most of the wallet types simultaneously.
For more information on what wallets are out there/what they have to offer, check out our Crypto Wallet Guide. Ready to buy on Binance, but not sure how? Read our guide on How to buy Crypto on Binance.














Responses