Some Vulnerabilities of Bitcoin’s Lightning Network
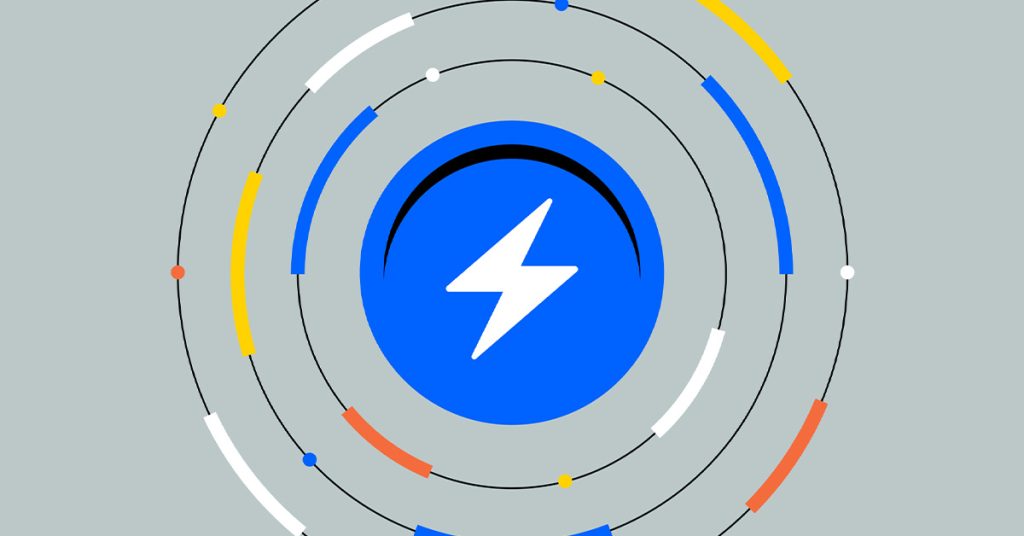
As Bitcoin’s Lightning Network usage has shot up even through the bear market – and it’s worth reminding ourselves of the near miracle it is: moving BTC across the world in seconds. – it’s still worth zooming in on the vulnerabilities.
There are still wrinkles to be ironed out. Usability and liquidity are two vulnerabilities of Bitcoin’s Lightning Network.
Before diving into the vulnerabilities and the potential solutions, let’s quickly recap what Lightning is.
Short Background on Lightning
The Lightning Network is a Layer 2 network that operates on a channel-based system. Two parties deposit funds to pay each other. This process saves them from having to wait for block confirmations before they can finalize transactions for goods or services. Even though it is not literally lightning-fast, settlement happens in a few seconds. It’s also cheap: think a penny.
Wait, isn’t the use case of opening a channel with one user very limited? Well, the person with whom you opened the channel has probably already other open channels. This means you’re only a handful of channels away from any person on earth that uses Lightning. Your payment flashes through a series of channels before it reaches its destination.
In short, the Lightning Network significantly improves Bitcoin’s scalability and transaction speed.
Some Lightning Usage Data
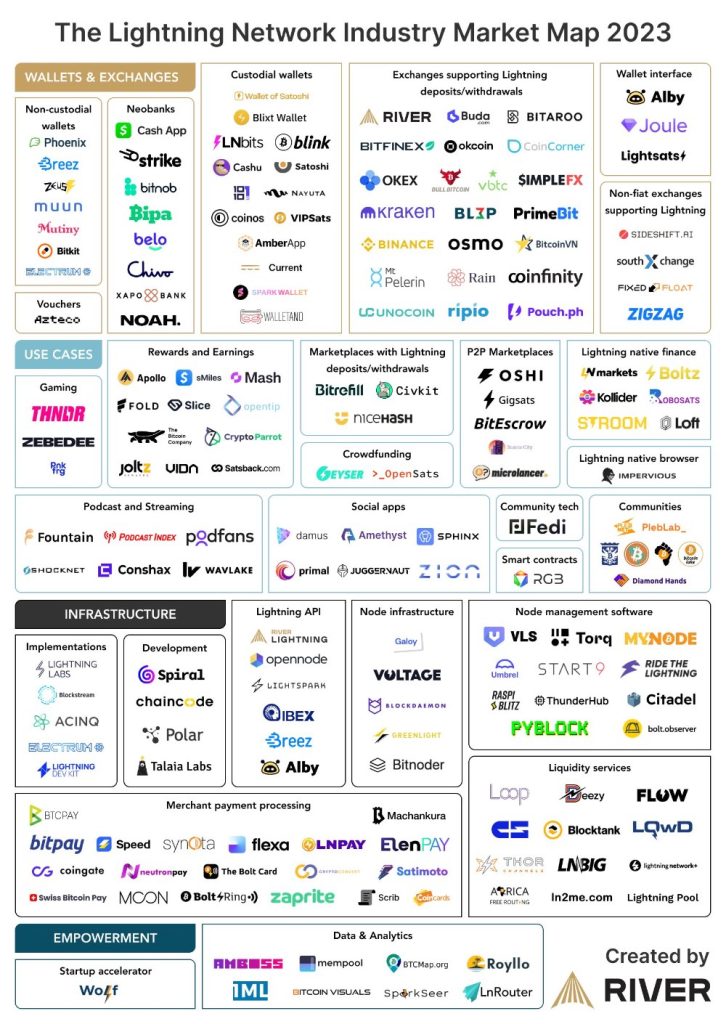
According to a report by Lightning company River, growth has been 1200% in two years, between August 2021 and August 2023.
Some other data points from the report:
- In August 2023 the average transaction volume was 2.5 transactions per second. Some of the fastest-growing sectors that use Lightning: social tipping (think Nostr), streaming and gaming.
- The average Lightning transaction size was around 44.7k satoshis, or $11.84.
- In August 2023, an estimated $78 million was publicly routed. This is a 546% increase since August 2021 and translates to 900 million dollars in yearly volume.
- River’s Lightning payment success rate was 99.7% in August 2023 across 308k transactions.
- Around 180 companies are Bitcoin Lightning companies (see picture)
Vulnerability #1: Usability
Even though usability is not a vulnerability in the technical sense, I still mention it here. Bad usability might slow down adoption and hence interest from developers to keep improving the protocol.
A newbie that wants to use Lightning while keeping their own BTC keys, must install software to run their own Lightning node. They must ‘manually’ open a channel with a user to kick off their first transaction. While nowadays this software that allows you to do this (Umbrel, for example) is user-friendly, it’s still not something that the masses will do. Even for companies, it is probably a stretch to run their own nodes.
A much more popular alternative for the average Lightning-curious user is to download a Bitcoin/Lightning wallet app. Wallet of Satoshi, for example, is a mobile app for iOS and Android. BUT. It is a custodial wallet, which means that the app provider holds your funds on your behalf and handles all the technical aspects of the Lightning Network for you. Convenient, but not your keys…
Vulnerability #2: Failed Transactions
The issue that is in part responsible for failed transactions – and failed transactions are a no-go for any payment solution that wants to scale globally – is the lack of insight into liquidity in channels. In the context of Lightning nodes, liquidity means the ability to move funds.
When it comes to liquidity, the existing tooling for the Lightning Network is not very sophisticated. While there is a clear map of channels, the amount of BTC in a channel isn’t mapped out. This means that, especially for higher transaction amounts, the chance of a failed transaction increases. The 99.7% transaction success quoted above by River, depends on a skilled implementation and operational overhead. The maintenance of a Lightning node and associated liquidity management ask for significant efforts and resources, which can be prohibitive for businesses. This cycles back to the earlier point of usability.
The Solution to Liquidity/Failed Transactions and Usability
As mentioned, for companies that want to adopt Lightning it can be counterintuitive and hard to get a node going. It requires locking liquidity, finding nodes to connect to, and ensuring inbound liquidity for receiving payments.
The company Lightspark has come up with an enterprise solution that improves usability and solves liquidity issues. I mention Lightspark not because it sponsors me (I wish) but because its founder David Marcus is no other than the former president of Paypal.
Lightspark
The founder of Lightspark points to the fact that you could ask a random stranger for his email address and send him a message on the spot. But money? Maybe if he lives in the same country and/or uses the same payment app. Lightspark wants to solve this, both for individuals and for businesses.
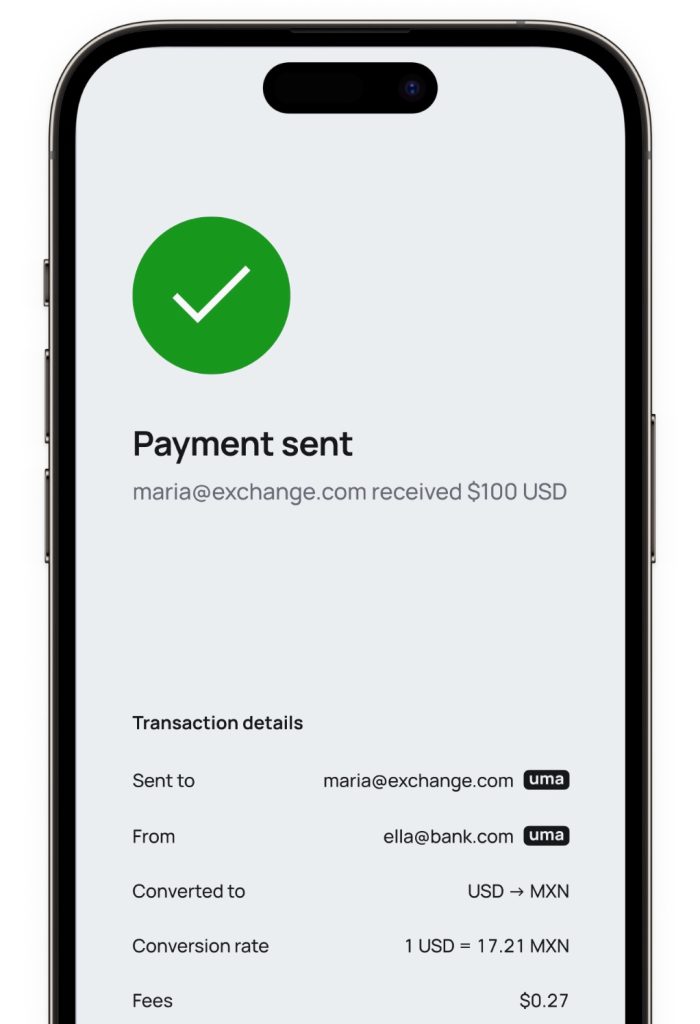
Note in the screenshot that Lightspark puts up an example in which it gets dollars across and converts these to MXN (Mexican peso). So, no BTC involved? Well, BTC is involved. The Lightning network is in this case only used as data rails for value, sent in BTC – but these sats can be converted on either end. This is also the way that Jack Mallers’ app Strike works, by the way.
The sent-to and from addresses in the above example are called: UMAs (Universal Money Addresses). They are like email addresses but for money. The UMA standard is open source and global. Anyone can send and receive money in any fiat or cryptocurrency using their favorite wallet, exchange, or bank. Lightspark has integrated this standard to combine human-readable Lightning Addresses with real-time, global payment rails. It extends the capabilities of Lightning to add support for compliance and fiat currencies.
(Currently, stablecoins on Lightning are another interesting development. This is technically fundamentally different from the above dollar example. Why? Because the stablecoins will travel tokenized on Lightning rails.)
Lightspark Predict
Lightspark Predict is a pillar of Lightspark and it solves the mentioned liquidity problem. Lightspark Predict generates a map of the entire Lightning network in terms of where the liquidity is, how good or bad the latency is, uptime, etcetera. With this data set it can apply liquidity where needed for Lightspark customers. This makes large transactions on Lightning possible. And the user doesn’t need to worry about it, it’s taken care of by Lightspark.
Vulnerability #3: Security Bugs
In October 2023, a Lightning developer announced a vulnerability so critical that he decided to quit. It was probably the first ‘rage quit’ from a Lightning developer in the history of Lightning!
What is this vulnerability? It has to do with the exploit of a function called ‘transaction replacement’, which is to remove one or more inputs of a multi-input transaction from node mempools.
Let’s say the two players involved in this multi-input transaction are malicious Alice and good old Bob. Alice can wait for Bob to spend his output, replace his spend with a spend of her own that contains an additional input, and then replace her spend with a transaction that no longer spends their shared output. This is called a replacement cycle.
Let’s face it, you and I don’t fully grasp this so-called ‘cyclical replacement vulnerability’: it’s a complex scheme. It can work as Alice knows what transaction Bob might want to transmit and owns one of the outputs. The current Lightning implementations allow for this attack, in which Alice keeps Bob’s transaction pinned in the mempool (that’s why these are called ‘pinning attacks’).
Dealing with this Bug
First, it’s important to understand that only nodes being used to forward payments are affected. In other words, users who only use their channels to initiate and receive payments are not affected.
But should we be worried in other cases? Not in the view of Bitcoin and Lightning expert Andreas Antonopoulos. Why? When it comes to security vulnerabilities there is always a difference between theoretical exploits and the ability to exploit such a vulnerability at scale in a way that would undermine the network.
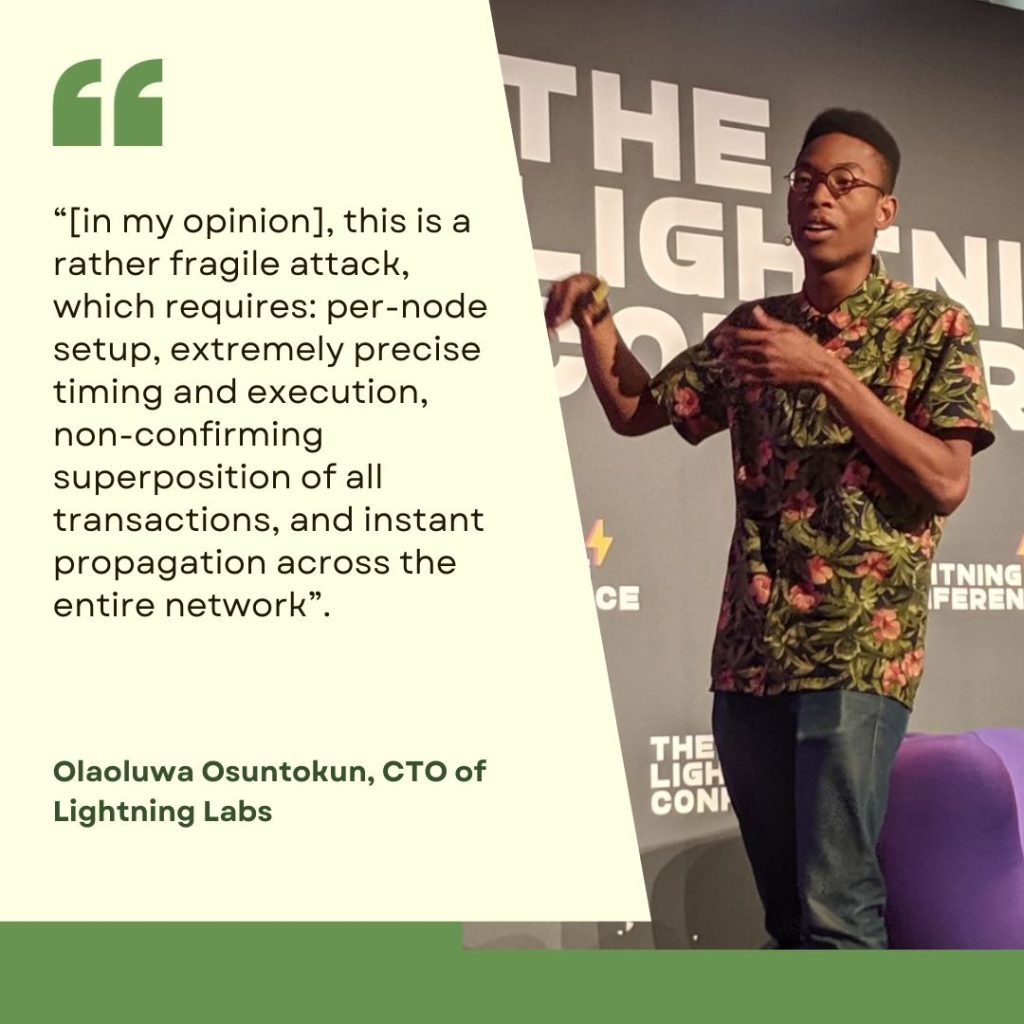
Olaoluwa Osuntokun, CTO of Lightning Labs, argued, “[in my opinion], this is a rather fragile attack, which requires: per-node setup, extremely precise timing and execution, non-confirming superposition of all transactions, and instant propagation across the entire network”.
Already, mitigations have been introduced in the latest iteration of Bitcoin’s C-Lightning and several other implementations.
The attack possibility is not a good thing, of course, but it certainly is not the end. It will require Lightning devs to construct mitigations and disincentivize these attacks by setting up penalties. (if you want to nerd out on this bug, check this Bitcoin Optech newsletter).
Conclusion
Even though Bitcoin’s Lightning Network works remarkably well – considering that it provides near-instant settlement in ‘physical’ BTC (no IOU) in seconds – it is still too cumbersome to use and still too slightly unreliable. Untransparent liquidity and bad usability make it not ready for mass adoption. Bugs are still discovered. But adoption keeps increasing. And let’s face it, these are growing pains of any emerging technology. Literally, dozens of companies are solving these issues as we speak.